BPDU Filter vs BPDU Guard
Today we will try to explore the difference between these 2 options, BPDU guard and BPDU filter
We know that BPDU are used to communicate between switches in L2 networks to ensure loop free topology.
BPDU Guard is used to protect our access (or trunks incase of servers) ports from receiving undesired BPDU packets, this feature is helpful in enforcing your network boundary in access layer
BPDU Guard can be enabled on global configuration as well as under the interface configuration
BPDU Filter on the other hand is used to filter BPDU packets outbound when configured in global configuration (after sending 11 BPDU out ) and will filter BPDU inbound/outbound when configured under the interface level
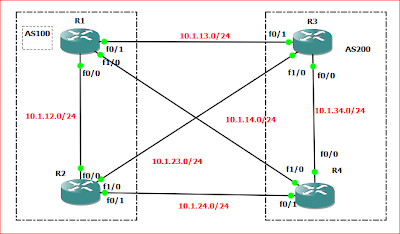
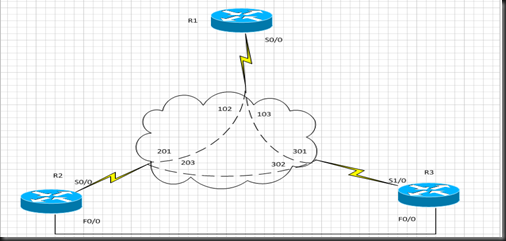
To better understand these two features, let’s use this simple topology
R1 is connected to SW1 through F0/0 to have R1 send and receive BPDU we will simple configure bridging group 1 on the router and we will join the bridge group when desired to test our configuration
BPDU Guard in global configuration
| SW1(config)#do sh run | in span spanning-tree mode pvst spanning-tree portfast default spanning-tree portfast bpduguard default |
The above commands will put all access ports into portfast mode and configure BPDU Guard on all portfast interfaces
And we will configure f0/1 as access port
| SW1(config)#do sh run interf f0/1 Building configuration... Current configuration : 57 bytes ! interface FastEthernet0/1 switchport mode access end |
Before we configure anything on R1 we will check the portfast status of that interface f0/1 on the switch
SW1(config)# do sh span interf f0/1 port VLAN0001 enabled |
As we see we portfast is enable as expected
Now let’s configure the bridging group on R1
| R1(config)#bridge 1 protocol ieee R1(config)#interf f0/0 R1(config-if)#bridge-group 1 |
The moment you will configure these commands on R1, you should see the following on SW1
| SW1(config)# *Mar 1 02:38:57.930: %SPANTREE-2-BLOCK_BPDUGUARD: Received BPDU on port Fa0/1 with BPDU Guard enabled. Disabling port. SW1(config)# *Mar 1 02:38:57.930: %PM-4-ERR_DISABLE: bpduguard error detected on Fa0/1, putting Fa0/1 in err-disable state SW1(config)# *Mar 1 02:38:58.962: %LINEPROTO-5-UPDOWN: Line protocol on Interface FastEthernet0/1, changed state to down SW1(config)# *Mar 1 02:38:59.960: %LINK-3-UPDOWN: Interface FastEthernet0/1, changed state to down |
AS we can see from the output above the switch has put the interface in err-disabled mode because it received BPDU packets while BPDU Guard is enabled in global configuration
Now let’s move to the second way of configuring BPDU Guard
BPDU Guard under interface level
remove previous configuration and apply the BPDU guard under the f0/1 on SW1
| SW1(config)#do sh run interf f0/1 Building configuration... Current configuration : 89 bytes ! interface FastEthernet0/1 switchport mode access spanning-tree bpduguard enable |
Now let’s join R1 F0/0 interface to bridge group 1
| *Mar 1 00:53:45.730: %SPANTREE-2-BLOCK_BPDUGUARD: Received BPDU on port Fa0/1 with BPDU Guard enabled. Disabling port. SW1(config-if)# *Mar 1 00:53:45.730: %PM-4-ERR_DISABLE: bpduguard error detected on Fa0/1, putting Fa0/1 in err-disable state SW1(config-if)# *Mar 1 00:53:46.761: %LINEPROTO-5-UPDOWN: Line protocol on Interface FastEthernet0/1, changed state to down SW1(config-if)# *Mar 1 00:53:47.760: %LINK-3-UPDOWN: Interface FastEthernet0/1, changed state to down |
Sure enough, once we join the interface to the bridging group, the switch interface will go down because of the bpdu that it has received
Now let’s BPDU Filter
BPDU Filter in global configuration
| SW1(config)#do sh run | in spann spanning-tree portfast default spanning-tree portfast bpdufilter default |
shutdown the port and clear the spanning tree counters on that interface
| SW1(config)#interf f0/1 SW1(config-if)#sh SW1(config)#do clear span counters interf f0/1 |
Now un-shut the port on SW1 and check the spanning tree details for that interface
| SW1(config)#do sh spann interf f0/1 deta Port 3 (FastEthernet0/1) of VLAN0001 is root forwarding Port path cost 19, Port priority 128, Port Identifier 128.3. Designated root has priority 32768, address 0013.19dc.aba0 Designated bridge has priority 32768, address 0013.19dc.aba0 Designated port id is 128.4, designated path cost 0 Timers: message age 2, forward delay 0, hold 0 Number of transitions to forwarding state: 1 Link type is point-to-point by default BPDU: sent 12, received 3 |
As we see the BPDU filter under global interface didn’t disable spanning tree completely under that interface, the moment the interface receives BPDU on that interface the interface will lose its role as portfast and start going through the normal phases of spanning tree process
so what happens if we remove the bridging group from R1, let’s see this
shutdown and clear the spanning tree counters on F0/1 again, remove bridging group from R0/0
un shut the port and let’s check spanning tree on that interface
| SW1(config-if)# do sh span interf f0/1 de Port 3 (FastEthernet0/1) of VLAN0001 is designated forwarding Port path cost 19, Port priority 128, Port Identifier 128.3. Designated root has priority 32769, address 000f.3478.1100 Designated bridge has priority 32769, address 001b.2b7e.9880 Designated port id is 128.3, designated path cost 19 Timers: message age 0, forward delay 0, hold 0 Number of transitions to forwarding state: 1 The port is in the portfast mode by default Link type is point-to-point by default Bpdu filter is enabled by default BPDU: sent 11, received 0 |
So we see that switch has sent exactly 11 BPDU out and it will stop untill it received a BPDU on that interface and then the port will lose its role as portfast
| SW1(config-if)#do sh span interf f0/1 port VLAN0001 enabled |
BPDU Filter under interface
remove previous configuration and configure the interface with bpdu filter
| SW1(config)#interf f0/1 SW1(config-if)#spanning-tree bpdufilter enable |
now let’s un-shut the interface and check the spanning tree counters
| SW1(config)#do sh span interf f0/1 de Port 3 (FastEthernet0/1) of VLAN0001 is designated forwarding Port path cost 19, Port priority 128, Port Identifier 128.3. Designated root has priority 32769, address 000f.3478.1100 Designated bridge has priority 32769, address 001b.2b7e.9880 Designated port id is 128.3, designated path cost 19 Timers: message age 0, forward delay 0, hold 0 Number of transitions to forwarding state: 1 The port is in the portfast mode by default Link type is point-to-point by default Bpdu filter is enabled BPDU: sent 0, received 0 |
As we can see BPDU sent/received is both Zero
while if we check R1 spanning tree counters we would see that R1 is actually sending BPDU out to SW1 and they are getting filtered
| R1#show spanning-tree interface f0/0 Port 4 (FastEthernet0/0) of Bridge group 1 is forwarding Port path cost 19, Port priority 128, Port Identifier 128.4. Designated root has priority 32768, address 0013.19dc.aba0 Designated bridge has priority 32768, address 0013.19dc.aba0 Designated port id is 128.4, designated path cost 0 Timers: message age 0, forward delay 0, hold 0 Number of transitions to forwarding state: 1 BPDU: sent 336, received 0 |
Couple of minutes later
| R1#show spanning-tree interface f0/0 Port 4 (FastEthernet0/0) of Bridge group 1 is forwarding Port path cost 19, Port priority 128, Port Identifier 128.4. Designated root has priority 32768, address 0013.19dc.aba0 Designated bridge has priority 32768, address 0013.19dc.aba0 Designated port id is 128.4, designated path cost 0 Timers: message age 0, forward delay 0, hold 0 Number of transitions to forwarding state: 1 BPDU: sent 358, received 0 |
So spanning tree bpdu filter under the interface does filter in/out bpdu under that interface
If you configure bpdu filter and bpdu guard under the same interface, bpdu filter will take precedence over bpdu guard since the bpdu will be filtered before they are detected by the bpdu guard
If you configure bpdu filter and bpdu guard in global configuration, they both will perform their own roles, bpdu filter will send 11 bpdu packets out the interface and if no response it will stop sending bpdu out, however if bpdu packets are to be received over the interface bpdu guard will kick in that case and put the port in err-disable mode
Comments
Post a Comment